Servicios

Administrados
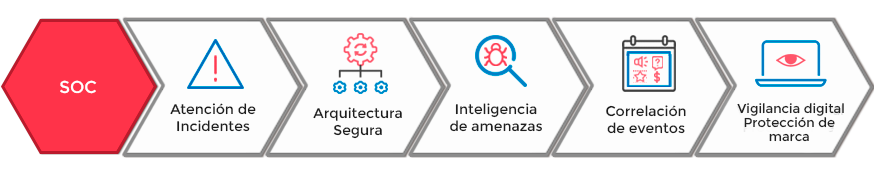
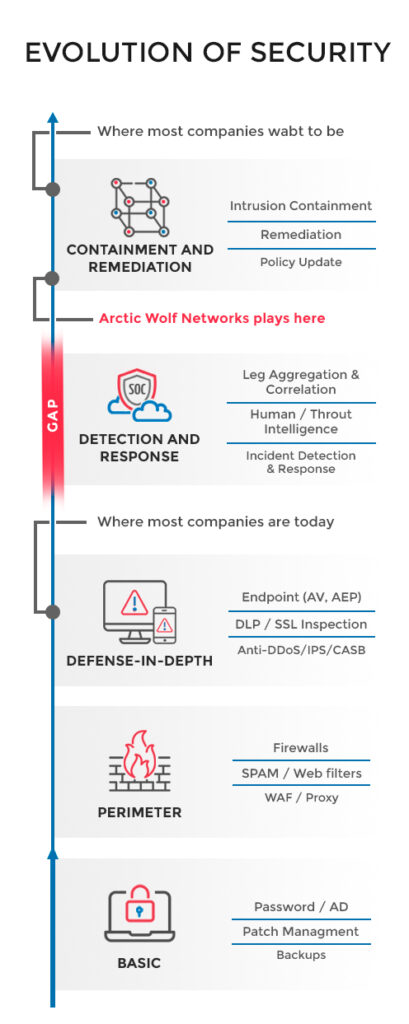
Las empresas que están en constante mejora de controles de seguridad necesitan un aliado estratégico de MDR (Manage Detect and Response).
Ofrecemos a nuestros clientes la tranquilidad de tener su infraestructura tecnológica monitoreada las 24 horas del día, los 365 días del año y en idioma español.

Este servicio de monitoreo y análisis busca minimizar riesgos informáticos, reducir costos, mitigar los incidentes de seguridad y facilitar la gestión de la seguridad informática.
Nuestro propósito no se trata solo de tecnología, sino también del servicio y la eficiencia que aportamos a través de ella, con el fin de impactar positivamente a cada dimensión de la compañía. Un trabajo conjunto que se ve reflejado en el cumplimiento de los objetivos de la organización.
Nuestro modelo de servicios está enfocado en optimizar sus procesos con el fin de que sus empleados puedan centrar todo su potencial explícitamente en el cumplimiento de los objetivos de negocio, evitando tener que enfrentarse con problemas cotidianos que afectan la productividad.
NUESTROS PRINCIPALES SERVICIOS


Administración Delegada
Administración de Plataformas de TI: Servicio permite a nuestros clientes delegar sus servicios de TI para apoyar labores misionales. Ofrecemos gestión integral de la infraestructura tecnológica.
NOC Monitoreo: Servicio que permite a nuestros clientes liberar sus recursos de TI para el apoyo de actividades misionales. Ofreciendo monitoreo, control, resolución de problemas en redes y mantenimiento.
Assessment: Servicio que permite a nuestros clientes evaluar su postura de seguridad en cuanto a configuración de sus elementos de TI
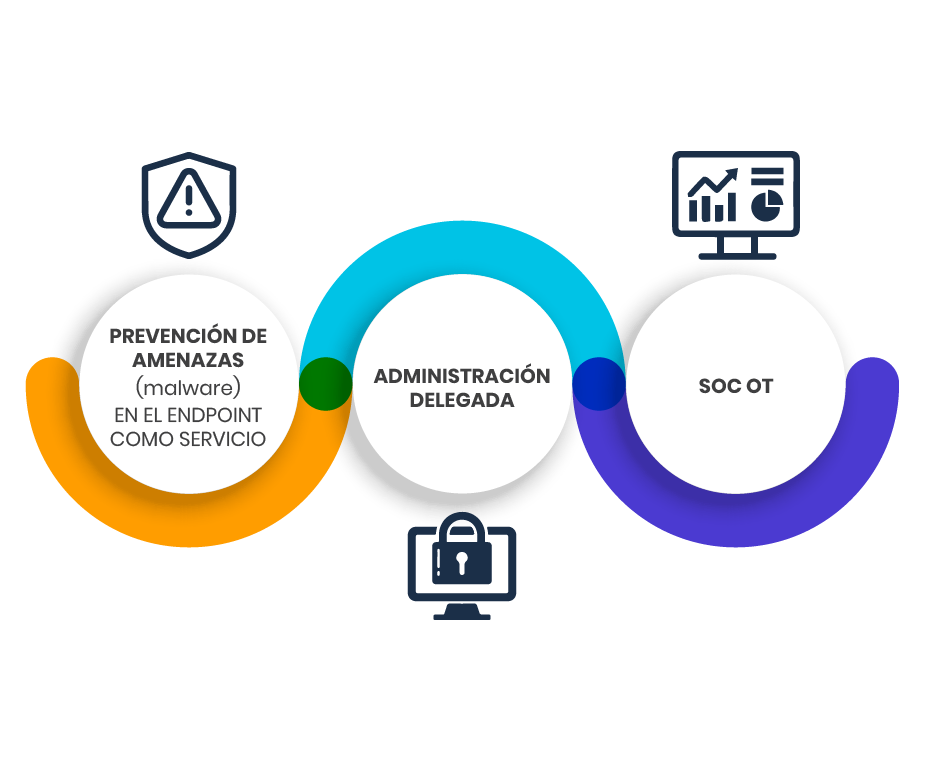
SOC
Atención de Incidentes: Servicio orientado a la detección temprana de incidentes por medio de la identificación y análisis de eventos de seguridad de la información.
Arquitectura Segura: Servicio orientado a la implementación de diseños y revisión de las arquitecturas de seguridad en los sistemas y redes de nuestros clientes.
Inteligencia de Amenazas: Servicio que prestamos a través de nuestro centro de servicio en modalidad 24/7, donde realizamos monitoreo inteligente de eventos e incidentes de seguridad de la información, por medio de la gestión de indicadores de compromiso.
Correlación Eventos: Servicio orientado a la correlación de datos de seguridad con el fin de identificar posibles incidentes que ocurran en los sistemas y redes de datos.
Vigilancia Digital/Protección de Marca: Servicio que provee detección de hechos o eventos de seguridad que pueden afectar el buen nombre de nuestros clientes por medio de suplantación de imagen, robo de información y datos de una marca y otros escenarios de ciberataques.
Ethical Hacking
Análisis de Vulnerabilidades: Servicio que Identifica vulnerabilidades técnicas que podrían explotar los ciberdelincuentes por medio de herramientas especializadas y licenciadas, Desarrollando e implementando procedimientos para el cierre de vulnerabilidades en los diferentes ambientes de nuestros clientes.
Pruebas de Intrusión: Servicio orientado a la ejecución de pruebas de explotación de vulnerabilidades simulando el actuar de un cibercriminal por medio del personal experto con el que cuenta Rsec Group.
Ingeniería Social: Servicio orientado a identificar problemas en la gestión de la seguridad de la información. Evaluación del comportamiento humano ante ataques dirigidos a personas de la organización, identificando fortalezas y debilidades sobre el cumplimiento de políticas de seguridad
Evaluación de Código: Servicio orientado a analizar código de aplicaciones de cliente, para la detección de errores, vulnerabilidades y malas prácticas en el proceso de desarrollo, desde una perspectiva de seguridad.
TRABAJAMOS CON LAS MARCAS DE TECNOLOGÍA MÁS RECONOCIDAS DEL MERCADO